Securing your passwords (and in result your digital ID)
Passwords originate from ancient times (like tech generally) with military context. They are used to confirm that the you are person you are claiming to be, as only you know the secret.
“Halt, who goes there”
“It is me, Romulus”
“What is the password?"
“Ananas!"
“Proceed!”
When you think of it, doing authentication this way still in 2020 seems rather silly. Nevertheless, as the world and it’s services are getting digitalised, an essential part of securing your digital identity is securing your passwords. And there is no reason not to secure your passwords, as you can get pretty far just by using free tooling. It’s only after you start dreaming about tin-foil-hats you have to pay for the extra security, and even then it’s just a few flimsy euros per month.
My recommendation for people securing their passwords:
| For | Methods |
|---|---|
| Everyone (yes, including your mom) | Good passwords, Password Manager |
| IT professionals | All the previous + Two-step auth, Reacting to breaches |
| Admins / people invested on the subject | All the previous + separation of devices providing authentication information |
TOC
About passwords
What do I mean by securing a password
Securing a password is not just having a secure password. A secure password is something that is hard for random people to guess and also hard for a computer to break. This is essential, but far from enough.
In addition we have to make sure that the attack vector for a single password is small, so we use only one password per service. This way if we use a password on a site that gets hacked and our credentials stolen, those credentials can’t be used elsewhere. This isn’t even far fetched scenario, as security breaches happen often, and sometimes with grave consequencies.
Good passwords
XKCD put the essentials on good password into one great picture (that is widely referenced):
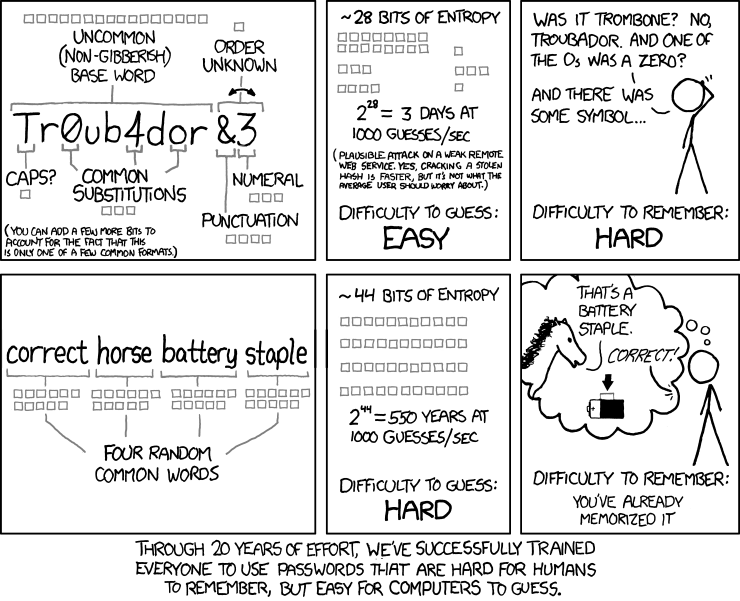
Basically: just use a phrase and forget all the special letters in passwords. If you want to go the extra mile (not really required, but makes you feel special): use non-English with conjugations
Tools & methods
Password manager
Password manager is the best thing that came out of the oven since sliced bread. With a password manager you put all your other passwords behind a master password, so you only have to remember just one. Password managers tend to have handy browser plugins, mobile apps etc. that automatically fill your passwords to sites for ease of access. They also have nice “generate me a secure password”-buttons, so you can easily create incomprehensible passwords for all of your logins, keeping the passwords unique. So implementing one does not only make you more secure, but it also comes with ease of access. That’s win-win if I see one.
Password managers are in plenty, and personally I’ve gotten stuck with Lastpass. If you are not using a password manager yet, a little bit of internet searching can also find you nice comparisons like this so you can find the one that fits you the best.
Two-step authentication
Our friend Wikipedia says it the best:
Two-step verification or two-step authentication is a method of confirming a user’s claimed identity by utilizing something they know (password) and a second factor other than something they have or something they are. An example of a second step is the user repeating back something that was sent to them through an out-of-band mechanism (such as a code sent over SMS), or a number generated by an app that is common to the user and the authentication system.
I would recommend activating two-step authentication on anything that might bite your arse if compromised, basically containing anything that is worth stealing: games, documents or passwords. If given the option, I would use One Time Passwords (OTPs) over SMSs or service app specific authentication, as phone numbers can be hacked and tend to change now and then, and a plethora of service apps just for authentication is a pain.
Strong suggestion on OTPs goes to Authty, for being The Better Google Authenticator. You can use it everywhere where Google Authenticator is supported, but unlike Google Authenticator supporting sync across devices, so your MFAs don’t go with your phone if you a) lose it b) change employers c) other. There is also a completely open source OTP-tool called andOTP for Android.
Important: If you use Authy with multiple devices, toggle the “Allow multi device” on only for the duration of adding your devices. If left ‘on’, Authy is vulnerable in case your mobile phone number is compromised.
Reacting to breaches
Reacting to data breaches is generally a good idea. There might have been something on the compromised site of value (bank credentials, etc.) that would require remediating, or you might just want to close the door for the hackers by replacing the password (taken that you still get in). If you are using a unique password everywhere (like you should), the hack won’t compromise other accounts, but your email address will probably be on a few new spam-lists.
There are (free) sites like badrap and haveibeenpwned where you can register your e-mail-address, and they will notify you if the address was compromised in a breach. Some password managers also have this notification feature built-in.
Stuff that exists, and I don’t like
“Free” single sign-ons (SSOs)
Concept is simple: you sign into one place, and you can use that authentication to pass your information to other places. The usual suspects on providing these services are Facebook, Google and Microsoft. Security-wise far better option than reusing your username/password-combination everywhere, and these authentication services tend to also support two-step-authentication out-of-the-box.
But here is the catch: if the service provided is free, you are the product being sold. So most probably all the information on my logins is stored for the service provider’s later marketing / reselling endeavours. Also not every service supports SSO, so this is not a silver bullet.
Rotating passwords
I don’t really get the point of password rotation, and I guess I’m not the only one. If it’s a password you regularly have to type (computer login for example), and thus want to remember by heart, people tend to be lazy and just add some running number at the end to be happy and comply.
Maybe someone can enlighten me on this subject, but I don’t get it. I just think they are a pain.
Digging deeper
Separation of authentication software
Some password managers provide, in addition to storing passwords, also the feature of directly providing OTPs. This is super handy, as you now have to use only one software and you get the full benefit. Hacking your credentials to the end services has become far more difficult.
But I still wouldn’t use them. Separating the OTP and password on two separate services protects from the case when supposedly your password manager would fail you. This might be due to a hack on the password manager service, your own negligence or a hack directed at you.
Separation of authenticating devices
Case 1:
Let’s say that you use a password manager on your computer, and have proved it with two-step authentication using OTPs on your mobile phone. All is nice and dandy: either your phone or laptop gets compromised and no passwords leak out.
Case 2:
You get bored of checking your passwords from your computer screen and typing them into your mobile on login, and decide to install the password manager also on your mobile (after all, there is a handy app for that). Now both the password manager and the method to secure it reside on the same mobile device making it the weakest link on your password strategy. The weakest link is carried around by you, making it easy to steal, and as you like things easy to use, it’s protected by your fingerprints.
Solution? Just think for a moment where your passwords are and where the second step for the authentication is, and do not put all the beans in the same bag. Security Keys are somewhat handy for this purpose, as they can be used for two-step authentication for Password Managers.
NOTE: Even if the password manager and OTP app would reside on the same computer / mobile / etc., it’s still by far better solution than leaving the two-step authentication completely out of the picture.
Security keys
The premise is simple: in addition to authenticating with your password, you also authenticate with something you own; the security key. Basically you plug an USB-dongle to the device you want to use for authentication (your computer or phone) and after password auth you commence two-step authentication by (gently) pushing the button on the side of the dongle. As the USB- security key is registered just as a USB-keyboard, it writes the OTP to where your cursor is.
There aren’t too many vendors of security keys. The most popular one is Yubikey, but recently Google launched their own Titan-series. Personally I’ve gone the Yubikey-route, as I’ve tried actively to steer away from everything Google. Feature-wise the competitors are pretty much the same. The keys cost around 50€/piece, and enabling them on Password Managers usually require you to have a premium subscription (around 3€/month).
Physical security key is something you can lose, or break, so I suggest having two. One that you carry with you and one that is in a Secure Place. You can’t clone your key (they are unique), so you can’t make the second one a real ‘backup’, but many sites & services support multiple security keys. Losing one is not a catastrophe, granted that you have registered them both for the services used.
Unique usernames (dumb idea)
Very often on web-services your email address is your username, paired with a password; in order to log in, you have to know both. So what if you could use a new email address for every service you register to?
Well, you can. Is it really really necessary? Is it kinda security through obscurity? Yes. Did I do it anyways? Of course.
You’ll need your own domain and a mail service that supports mail forwarding with wildcards. Gandi provides all that with reasonable pricing (~20€/a for .eu domain), and that my friend, is awesome-sauce.
To get rolling:
- Create an email forwarding rule
application*@yourdomain.comand a forward to youridontrevealthismailtoanyone@yourdomain.com - Set up all new new accounts with their own unique address: for Linkedin you just register as
applicationlinkedin@yourdomain.comand the mails get forwarded to your “backend mail address” with the original headers intact, allowing categorization.
Additional bonus: you get to know which site has sold your email address when you get spam mail at your application-specific email address. And because of GDPR, you can give them hell about it.